Data Protection and Privacy Act Compliance for Australian SMBs

Introduction
The Privacy Act 1988 and its amendments directly affect how Australian SMBs collect, store, use, and protect personal information. With the reforms that came into effect this year increasing compliance obligations and penalties, understanding your requirements is more important than ever.
This isn’t just about avoiding fines—though those have increased significantly. Good data protection practices build customer trust, reduce risk of costly breaches, and align with increasingly privacy-conscious consumer expectations.
This guide provides practical, implementable privacy compliance advice for Australian small businesses handling personal information.
Who Does the Privacy Act Apply To?
The Basic Rule
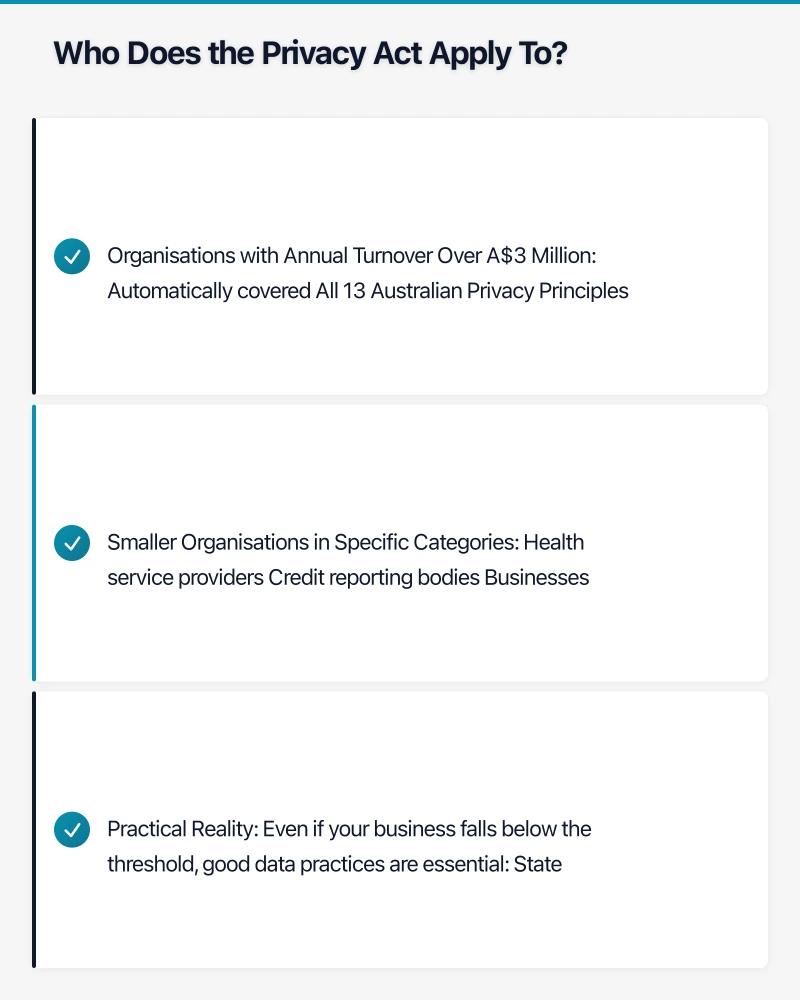
The Privacy Act applies to:
Organisations with Annual Turnover Over A$3 Million
- Automatically covered
- All 13 Australian Privacy Principles apply
- Notifiable Data Breach scheme applies
Smaller Organisations in Specific Categories
- Health service providers
- Credit reporting bodies
- Businesses trading in personal information
- Contracted service providers to Commonwealth
- Businesses that opted in
Practical Reality
Even if your business falls below the threshold, good data practices are essential:
- State privacy laws may apply
- Contractual requirements from larger clients
- Future growth may trigger obligations
- Consumer expectations regardless of legal requirements
- Risk management best practice
For this guide, we’ll assume your business is covered or chooses to follow privacy best practices.
The Australian Privacy Principles (APPs)
The 13 APPs govern how personal information must be handled. Here’s what each means for Australian SMBs:
APP 1: Open and Transparent Management
Requirement: Have a clearly expressed privacy policy
What You Need
- Privacy policy on your website
- Policy must be free and easily accessible
- Must describe what information you collect and why
- Must explain how information is stored and protected
- Must detail how people can access or correct their information
- Must explain how to complain
Practical Implementation
- Draft a privacy policy (templates available from OAIC)
- Link prominently on your website (usually in footer)
- Review and update annually
- Train staff on policy contents
APP 2: Anonymity and Pseudonymity
Requirement: Allow people to not identify themselves where practical
What You Need
- Offer anonymous options where feasible
- Don’t require identification unless necessary
- Consider if you really need that information
Practical Implementation
- Review forms and data collection
- Remove unnecessary identification requirements
- Allow enquiries without requiring name where appropriate
APP 3: Collection of Solicited Personal Information
Requirement: Only collect necessary information by lawful and fair means
What You Need
- Collect only what you actually need
- Collect directly from the individual where possible
- Get consent for sensitive information
- Don’t collect information through deception
Practical Implementation
- Audit what data you collect
- Remove unnecessary fields from forms
- Document why each piece of data is needed
- Establish consent processes for sensitive information
APP 4: Dealing with Unsolicited Personal Information
Requirement: Handle information you receive but didn’t ask for appropriately
What You Need
- Assess if you could have collected it directly
- If not, and you don’t need it, destroy it
- If you keep it, treat it according to APPs
Practical Implementation
- Train staff on handling unsolicited information
- Establish process for assessing unsolicited data
- Secure destruction procedures
APP 5: Notification of Collection
Requirement: Tell people what you’re collecting and why
What You Need
- Notify people when you collect their information
- Explain what you’ll do with it
- Identify who you might share it with
- Explain how they can access or correct it
Practical Implementation
- Privacy notices at point of collection
- Collection notices on forms
- Verbal notification where appropriate
- Staff training on notification requirements
APP 6: Use or Disclosure
Requirement: Only use or share information for the purpose it was collected
What You Need
- Use information only for stated purposes
- Get consent for other uses
- Limited exceptions (law enforcement, safety, etc.)
- Keep records of disclosures
Practical Implementation
- Document purposes for each data type
- Get explicit consent for marketing
- Establish process for disclosure requests
- Train staff on permitted uses
APP 7: Direct Marketing
Requirement: Specific rules for using personal information for marketing
What You Need
- Consent required for direct marketing (generally)
- Easy opt-out mechanism
- Honour opt-out requests promptly
- Don’t use sensitive information for marketing
Practical Implementation
- Obtain clear marketing consent
- Maintain opt-out list
- Process opt-outs within reasonable time (days, not weeks)
- Audit marketing lists against opt-outs
APP 8: Cross-Border Disclosure
Requirement: Ensure overseas recipients protect information appropriately
What You Need
- Take reasonable steps to ensure overseas compliance
- Inform individuals about overseas disclosure
- Consider using contractual protections
- You remain accountable for overseas recipients
Practical Implementation
- Identify overseas data transfers (cloud services, support)
- Document safeguards for each overseas recipient
- Consider data residency options for cloud services
- Include privacy clauses in vendor contracts
APP 9: Adoption, Use, or Disclosure of Government Identifiers
Requirement: Don’t use government IDs (TFN, Medicare) as your own identifiers
What You Need
- Don’t use government IDs as customer numbers
- Only collect government IDs when required
- Protect government IDs carefully
Practical Implementation
- Use your own identifier systems
- Limit collection of government IDs
- Extra security for stored government IDs
APP 10: Quality of Personal Information
Requirement: Keep information accurate, complete, and up-to-date
What You Need
- Take reasonable steps to ensure accuracy
- Keep information current for purposes used
- Correct inaccurate information
Practical Implementation
- Allow customers to update their information
- Regular data quality checks
- Process corrections promptly
- Don’t use outdated information for decisions
APP 11: Security of Personal Information
Requirement: Protect personal information from misuse, interference, loss, and unauthorized access
What You Need
- Implement appropriate security measures
- Consider sensitivity of information
- Destroy or de-identify when no longer needed
Practical Implementation
- See detailed security guidance below
- Regular security assessments
- Data retention and destruction policies
- Staff security training
APP 12: Access to Personal Information
Requirement: Give individuals access to their personal information
What You Need
- Provide access within reasonable time (30 days generally)
- Free or minimal cost
- Limited exceptions (legal, commercial confidence)
Practical Implementation
- Establish access request process
- Designate responsible person
- Track and respond to requests timely
- Document any refusals with reasons
APP 13: Correction of Personal Information
Requirement: Correct inaccurate information when requested
What You Need
- Correct information within reasonable time
- Notify third parties if previously disclosed
- Note if correction is disputed
Practical Implementation
- Process for receiving correction requests
- Ability to update records
- Notify relevant parties of corrections
- Document disputed corrections
The Notifiable Data Breach Scheme
What Constitutes a Notifiable Breach
A breach is notifiable if:
There Is a Data Breach
- Unauthorised access (someone who shouldn’t see data sees it)
- Unauthorised disclosure (data shared inappropriately)
- Loss of data (can’t locate or access data)
AND It’s Likely to Result in Serious Harm
Factors to consider:
- Type of information (sensitive info = more likely harmful)
- Who had access (criminal = more concerning than employee)
- Whether information is protected (encrypted = less harmful)
- Whether information can be used maliciously
Assessment Requirements
When you become aware of a potential breach:
30-Day Assessment Period
- Assess whether breach is notifiable
- Take steps to reduce harm
- Document your assessment
- Must complete within 30 days (or sooner if obviously notifiable)
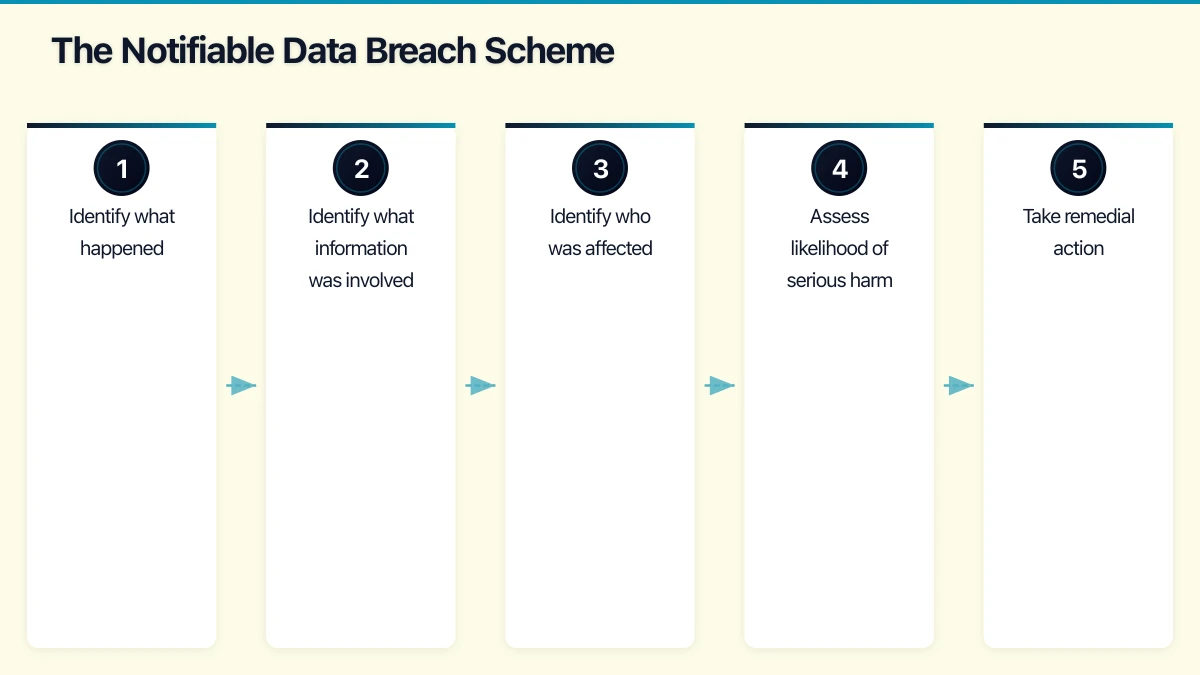
Assessment Steps
- Identify what happened
- Identify what information was involved
- Identify who was affected
- Assess likelihood of serious harm
- Take remedial action
- Document everything
Notification Requirements
If breach is notifiable:
Notify the OAIC
- As soon as practicable
- Statement including:
- Your identity and contact details
- Description of the breach
- Types of information involved
- Recommendations for affected individuals
Notify Affected Individuals
- As soon as practicable
- Same information as OAIC notification
- How you’ll contact them (email, letter, phone)
- If impractical to contact directly, publish notice
Recent Changes (2026)
The Privacy Act amendments effective this year have strengthened breach notification:
Increased Penalties
- Maximum penalty now up to A$50 million for serious/repeated breaches
- Or three times the benefit obtained
- Or 30% of adjusted turnover
- These are maximum penalties; smaller breaches attract smaller penalties
Enhanced OAIC Powers
- Expanded investigation powers
- Can require organizations to take specific actions
- Greater enforcement flexibility
Tighter Timeframes
- Assessment expectations more clearly defined
- Notification must be more prompt
Practical Implementation for Australian SMBs
Step 1: Data Mapping
Understand what personal information you hold:
Create a Data Inventory
| Data Type | Examples | Source | Storage | Access | Retention |
|---|---|---|---|---|---|
| Customer contact | Name, email, phone | Website forms | CRM (HubSpot) | Sales, support | 7 years after last contact |
| Employee records | Name, TFN, address | Employment forms | HRIS (Employment Hero) | HR, payroll | 7 years after employment ends |
| Financial data | Credit card, bank details | Payments | Xero, Stripe | Finance | 7 years |
Document Data Flows
- Where does data come from?
- Where does it go?
- Who can access it?
- Where is it stored (including backups)?
- Does it go overseas?
Step 2: Privacy Policy and Notices
Draft Your Privacy Policy
Include:
- Your identity and contact details
- Types of personal information collected
- How information is collected
- Purposes of collection
- How information is stored and secured
- Third parties information is shared with
- Whether information goes overseas
- How individuals can access and correct information
- How to make a complaint
Collection Notices
For each collection point (forms, sign-ups):
- Brief notice at point of collection
- Link to full privacy policy
- Specific notice for sensitive information
Step 3: Security Measures
Technical Controls
| Area | Minimum Standard | Better Practice |
|---|---|---|
| Access Control | Unique passwords, MFA for sensitive systems | MFA everywhere, role-based access |
| Encryption | HTTPS for websites, encrypted email for sensitive data | Encryption at rest and in transit |
| Endpoint Protection | Current antivirus | EDR solution |
| Backup | Regular backups | Encrypted, tested backups, offsite |
| Patching | Regular updates | Automated patching, prompt critical patches |
Administrative Controls
- Staff training on data handling
- Clear policies on acceptable use
- Incident response procedures
- Vendor assessment processes
- Regular security reviews
Physical Controls
- Secure offices (locks, access control)
- Clean desk policy
- Secure disposal of paper documents
- Visitor management
Step 4: Data Retention and Destruction
Establish Retention Periods
| Data Type | Retention Period | Source |
|---|---|---|
| Tax records | 7 years | ATO requirements |
| Employee records | 7 years after employment ends | Fair Work |
| Customer transactions | 7 years | Companies Act |
| Marketing contacts | Until opt-out or no longer needed | Privacy Act |
| Enquiries (not converted) | 2 years | Business practice |
Destruction Procedures
- Digital: Secure deletion, not just “delete”
- Paper: Cross-cut shredding
- Media: Certified destruction
- Document destruction and maintain records
Step 5: Incident Response
Prepare Before Incidents Happen
Incident Response Plan
- Identification: How will you detect breaches?
- Containment: How will you limit damage?
- Assessment: How will you assess notifiability?
- Notification: Who notifies whom, and how?
- Recovery: How will you restore normal operations?
- Lessons: How will you prevent recurrence?
Response Team
- Designate privacy officer (or equivalent)
- Identify IT/security responders
- Know when to engage legal counsel
- Have OAIC contact information ready
Documentation
- Incident log template
- Assessment checklist
- Notification templates
- Contact lists
Step 6: Ongoing Compliance
Regular Activities
| Frequency | Activity |
|---|---|
| Ongoing | Process access/correction requests within timeframes |
| Monthly | Review any incidents or near-misses |
| Quarterly | Staff awareness refresher |
| Annually | Privacy policy review |
| Annually | Data mapping update |
| Annually | Security assessment |
Training
All staff handling personal information should understand:
- What personal information is
- Why privacy matters
- Company policies and procedures
- How to recognise and report incidents
- How to handle access requests
Common Compliance Gaps
Gap 1: No Privacy Policy or Outdated Policy
The Problem: No privacy policy, or one that doesn’t reflect actual practices
The Fix:
- Draft or update privacy policy
- Ensure it reflects what you actually do
- Review annually and after significant changes
Gap 2: Overcollection
The Problem: Collecting information “just in case” or because forms have always asked for it
The Fix:
- Audit what you collect
- Remove unnecessary fields
- Ask “why do we need this?” for each item
Gap 3: No Retention Policy
The Problem: Keeping data forever, creating ongoing risk
The Fix:
- Establish retention periods
- Implement deletion processes
- Don’t keep what you don’t need
Gap 4: Inadequate Security
The Problem: Security measures don’t match data sensitivity
The Fix:
- Assess data sensitivity
- Implement appropriate controls
- Regular security reviews
Gap 5: No Incident Response Plan
The Problem: Scrambling when incidents occur, risking inadequate response
The Fix:
- Document response procedures
- Assign responsibilities
- Practice response scenarios
Gap 6: Unknown Data Flows
The Problem: Not knowing where personal information goes, especially overseas
The Fix:
- Map data flows
- Document third-party sharing
- Assess overseas transfers
Working with Cloud Services
Cloud Provider Assessment
When using cloud services that handle personal information:
Questions to Ask
- Where is data stored? (Australian data centres preferred)
- What security certifications do they hold?
- What are their privacy commitments?
- How do they handle data breaches?
- What happens to data on termination?
Common Cloud Services and Privacy
| Service | Australian Data Option | Privacy Assessment |
|---|---|---|
| Microsoft 365 | Yes (Sydney, Melbourne) | Strong privacy commitments |
| Google Workspace | Yes (Sydney) | Adequate for most SMBs |
| Xero | Yes | Australian company, local data |
| Salesforce | Yes | Strong privacy program |
| HubSpot | Limited | US-based, assess acceptability |
| Dropbox | Limited | US-based, consider alternatives |
Contractual Protections
For cloud services and other vendors handling personal information:
Include in Contracts
- Privacy obligations
- Security requirements
- Breach notification requirements
- Audit rights
- Subprocessor restrictions
- Termination and data return
Conclusion
Privacy compliance for Australian SMBs is achievable without excessive cost or complexity. The fundamentals are straightforward:
- Know what data you have and why you have it
- Tell people what you’re doing with their information
- Protect it appropriately with reasonable security
- Don’t keep it forever—delete when no longer needed
- Be prepared for incidents with a response plan
- Respect individual rights to access and correct their information
The Privacy Act reforms this year have increased the stakes, but they haven’t fundamentally changed what good privacy practice looks like. Australian SMBs that take a reasonable, documented approach to privacy compliance will be well-positioned.
Need help assessing your privacy compliance or implementing appropriate controls? CloudGeeks provides practical privacy and security assistance for Australian SMBs. Contact us for an obligation-free discussion.
