Cybersecurity Insurance: What Australian SMBs Need to Know in 2024

The call from your IT person at 7 AM is never good news. “We’ve been hit with ransomware. Everything’s encrypted.” For Australian SMBs, this scenario is becoming increasingly common—and increasingly expensive. Beyond the immediate technical response, there’s another question that determines whether this incident becomes a manageable setback or a business-ending catastrophe: do you have cybersecurity insurance?
With cyber attacks on Australian businesses up 23% year-on-year according to the Australian Cyber Security Centre’s latest threat report, and the average cost of a data breach now exceeding $3.35 million globally, cybersecurity insurance has moved from “nice to have” to “business critical” for SMBs. But navigating the Australian cyber insurance market can feel like learning a new language, filled with coverage gaps, exclusions, and prerequisites that catch many business owners off guard.
This guide breaks down everything Australian SMBs need to know about cybersecurity insurance in 2024—from understanding what’s actually covered to meeting insurer requirements and navigating the claims process when the worst happens.
Understanding Cybersecurity Insurance Coverage
Cybersecurity insurance (also called cyber liability insurance or cyber risk insurance) protects your business from the financial impact of cyber incidents. Unlike traditional business insurance that might cover physical theft or property damage, cyber insurance addresses digital risks.
What’s Typically Covered
First-Party Costs (damage to your own business):
- Business interruption: Lost revenue while systems are down, typically calculated based on your historical revenue
- Data recovery and restoration: Professional services to rebuild databases and restore systems from backups
- Ransomware payments: The actual ransom amount (controversial, but many policies include this)
- Cyber extortion: Payments to prevent data release or further attacks
- Crisis management: PR firms to manage reputation damage, notification costs to affected customers
- Legal and forensic investigation: IT forensics teams to determine breach scope and legal counsel for compliance
Third-Party Costs (liability to others):
- Privacy liability: Legal costs and settlements when customer data is compromised
- Network security liability: Claims from others affected by malware spreading from your systems
- Regulatory fines: Penalties under the Privacy Act 1988 (though some exclusions apply)
- Payment card industry (PCI) fines: Penalties for payment card data breaches
- Media liability: Defamation or copyright claims related to digital content
For Australian SMBs, a typical policy might offer $1 million to $5 million in coverage, with premiums ranging from $1,500 to $10,000 annually depending on your industry, revenue, and security posture.

Common Exclusions to Watch For
Understanding what’s not covered is equally important:
Infrastructure and software upgrades: If you’re running outdated systems, insurers won’t cover the cost of modernizing your infrastructure post-breach. That Windows Server 2012 you’ve been meaning to upgrade? Not covered.
Pre-existing vulnerabilities: If an attacker exploits a known vulnerability you haven’t patched, many policies exclude coverage. The 30-day-old unpatched Exchange Server vulnerability? You might be on your own.
Acts of war and nation-state attacks: The murky area of cyberwarfare is typically excluded. If your breach is attributed to state-sponsored actors, coverage may be denied.
Betterment costs: Insurers pay to restore to your previous state, not improve it. If you had basic backups, they won’t fund your upgrade to enterprise-grade backup solutions.
Intellectual property theft: Stolen trade secrets or source code often isn’t covered under standard policies.
Future lost revenue: While business interruption during downtime is covered, potential future revenue loss from reputation damage typically isn’t.
Australian-Specific Considerations
The Australian market has unique characteristics SMBs need to understand:
Privacy Act compliance: Since the 2022 amendments to the Privacy Act, businesses handling personal information face stricter requirements. While cyber insurance can cover some regulatory costs, intentional non-compliance isn’t covered. If the Office of the Australian Information Commissioner (OAIC) finds you willfully ignored your obligations, expect exclusions to apply.
Data sovereignty: Many Australian insurers require that backup data be stored within Australia or approved jurisdictions. Cloud backups in Singapore or Sydney AWS regions are typically fine; backups exclusively in US-only regions might trigger questions.
Notifiable Data Breaches (NDB) scheme costs: The cost of notifying affected individuals under the NDB scheme is usually covered, but insurers expect you to have processes ready to execute this quickly.
Policy Types and Coverage Levels
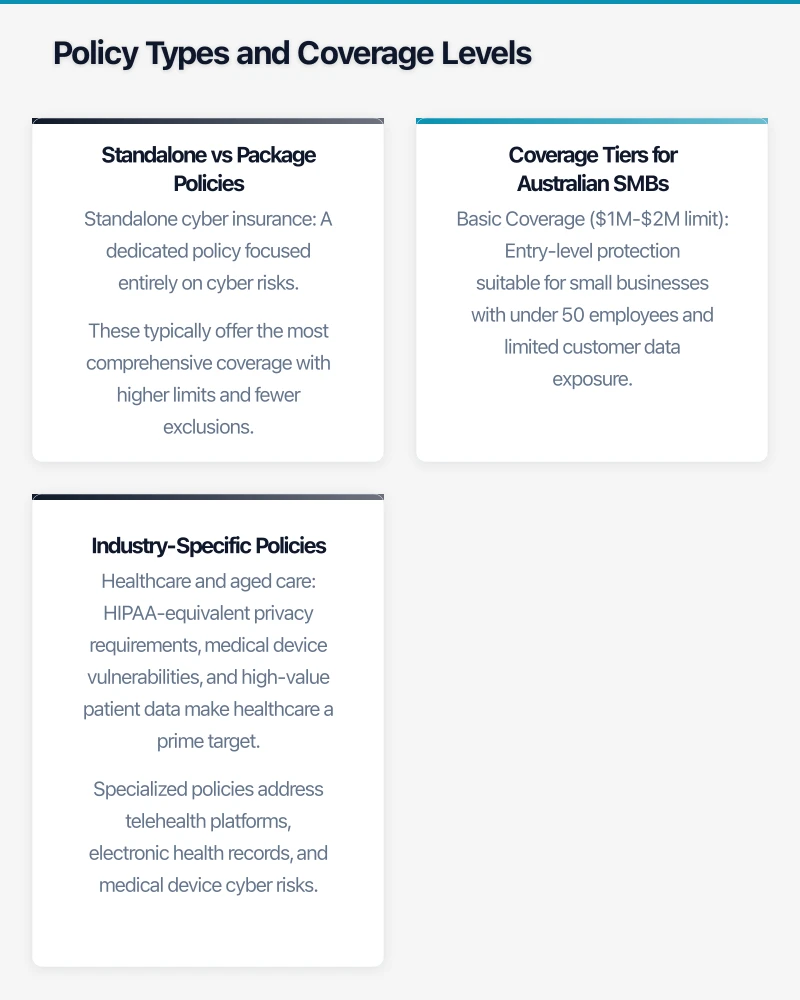
Not all cyber insurance policies are created equal. Understanding the tiers helps you match coverage to your actual risk.
Standalone vs Package Policies
Standalone cyber insurance: A dedicated policy focused entirely on cyber risks. These typically offer the most comprehensive coverage with higher limits and fewer exclusions. Best for businesses with significant digital exposure—e-commerce platforms, companies storing customer data, or those heavily dependent on cloud systems.
Cyber coverage endorsement: An add-on to your existing business insurance policy. More affordable but usually comes with lower limits (often $250,000 to $1 million) and more restrictive terms. Suitable for businesses with minimal digital footprint—think local tradies with just a website and basic email.
Technology Errors & Omissions (E&O) with cyber: For IT service providers and consultancies, combining professional liability with cyber coverage makes sense. If your advice or services lead to a client’s breach, you need both types of protection.
Coverage Tiers for Australian SMBs
Basic Coverage ($1M-$2M limit): Entry-level protection suitable for small businesses with under 50 employees and limited customer data exposure. Expect annual premiums of $1,500-$3,500. Coverage focuses on first-party costs with basic third-party liability. Good for professional services firms, small retailers, and local businesses.
Standard Coverage ($2M-$5M limit): The sweet spot for most Australian SMBs. Includes comprehensive first and third-party coverage, business interruption up to 12 months, and robust incident response support. Annual premiums typically $3,500-$8,000. Recommended for businesses storing customer payment information, healthcare providers, or companies with 50-200 employees.
Premium Coverage ($5M+ limit): For larger SMBs or those in high-risk sectors like healthcare, finance, or technology. Includes enhanced crisis management, elevated sub-limits for various costs, and potentially some coverage for nation-state attacks. Premiums from $8,000-$20,000+ annually.
Industry-Specific Policies
Certain sectors face unique cyber risks requiring specialized coverage:
Healthcare and aged care: HIPAA-equivalent privacy requirements, medical device vulnerabilities, and high-value patient data make healthcare a prime target. Specialized policies address telehealth platforms, electronic health records, and medical device cyber risks. Expect stricter security requirements and higher premiums.
Financial services: Handling customer financial data triggers additional regulatory scrutiny under APRA guidelines. Policies for financial advisors, mortgage brokers, and small lenders include higher limits for regulatory defense and social engineering fraud coverage.
E-commerce and retail: PCI DSS compliance is mandatory, and policies often include specific coverage for payment card data breaches. Higher limits for business interruption since online retailers can’t operate during attacks.
Legal and accounting firms: Client trust account data and sensitive financial records make these firms attractive targets. Coverage emphasizes professional liability intersection with cyber risks.
Real Costs: What Australian SMBs Are Paying
Premium pricing varies significantly based on risk factors insurers assess. Understanding these helps you both budget accurately and potentially reduce costs.
Premium Calculation Factors
Annual revenue: Larger revenue generally means more premium, though the relationship isn’t linear. A $5 million revenue business might pay $4,000 annually while a $20 million business pays $8,000—double the revenue doesn’t mean double the premium.
Industry and data sensitivity: Healthcare and finance pay 30-50% more than general professional services. Retailers handling payment cards pay 20-30% more than B2B service providers.
Employee count: More employees mean more endpoints and greater human error risk. Businesses with remote workers face additional scrutiny.
Security posture: This is where you can significantly impact premiums. Insurers assess:
- Multi-factor authentication (MFA) implementation
- Endpoint detection and response (EDR) solutions
- Regular employee security training
- Backup and disaster recovery procedures
- Patch management processes
- Cyber incident response plan documentation
Businesses meeting all security requirements can see premiums 25-40% lower than those with weak security controls.
Claims history: Like car insurance, previous cyber claims increase future premiums. Even claims with other insurers show up in industry databases. A ransomware claim might increase premiums 30-50% at renewal.
Typical Premium Ranges in 2024

Here’s what Australian SMBs are actually paying across different sectors:
Professional services (accounting, legal, consulting):
- 10-25 employees, $2M coverage: $2,000-$3,500/year
- 25-50 employees, $3M coverage: $3,500-$5,500/year
- 50-100 employees, $5M coverage: $5,500-$9,000/year
Healthcare (GP clinics, allied health, aged care):
- Small practice, $2M coverage: $3,000-$5,000/year
- Medium facility, $5M coverage: $6,000-$12,000/year
Retail and e-commerce:
- Small online retailer, $2M coverage: $2,500-$4,500/year
- Multi-channel retailer, $5M coverage: $5,000-$10,000/year
Technology and software companies:
- Startup/small dev shop, $2M coverage: $3,000-$6,000/year
- Established software company, $5M+ coverage: $8,000-$15,000/year
Deductibles and How They Impact Premiums
Deductibles (the amount you pay before insurance kicks in) significantly affect premium costs:
Low deductible ($2,500-$5,000): Expect premiums 20-30% higher. Makes sense for businesses with tight cash flow who couldn’t absorb a $25,000 out-of-pocket expense.
Standard deductible ($10,000-$25,000): The most common choice, balancing premium costs with manageable out-of-pocket exposure. This is where most Australian SMBs land.
High deductible ($50,000+): Can reduce premiums 30-40%, but you need sufficient reserves to cover this amount. Suitable for larger SMBs with strong balance sheets who want coverage mainly for catastrophic scenarios.
Some insurers offer “zero deductible” for specific services like crisis management hotlines or forensic investigation, recognizing that immediate response is critical.
Prerequisites: What Insurers Require Before Covering You
The days of easy cyber insurance are over. Following major ransomware incidents and significant insurer losses, the underwriting process has become rigorous. Here’s what you need in place before insurers will even quote you.
Mandatory Security Controls
These aren’t suggestions—they’re deal-breakers. Without these, expect declined applications or severely limited coverage:
Multi-Factor Authentication (MFA): Must be implemented on all remote access points, cloud email (Microsoft 365, Google Workspace), and privileged accounts. SMS-based MFA is increasingly insufficient; insurers prefer authenticator apps or hardware tokens. If you’re still using just passwords for Office 365 access, you won’t get covered.
Endpoint Detection and Response (EDR): Traditional antivirus isn’t enough. Insurers want behavior-based threat detection on all endpoints. Solutions like Microsoft Defender for Business, CrowdStrike, SentinelOne, or Sophos Intercept X are standard requirements. Budget $5-15 per endpoint per month.
Regular backups with offline/immutable storage: Backups must be:
- Tested regularly (quarterly minimum)
- Stored offline or in immutable cloud storage
- Retained for at least 30 days
- Include all critical systems and data
That external hard drive sitting next to your server? Not sufficient. Cloud-only backups without immutability? Also insufficient. Insurers want backups that ransomware can’t encrypt.
Patch management process: Systems must be patched within 30 days of critical security updates release. This applies to operating systems, applications, and network devices. Many insurers now require automated patch management tools with reporting.
Email security: Advanced email filtering beyond basic spam protection. Features like anti-phishing, attachment sandboxing, and URL rewriting are expected. Microsoft Defender for Office 365 or similar third-party solutions.
Documentation Insurers Want to See
Written information security policy: A documented policy covering:
- Acceptable use of systems
- Password requirements
- Data handling procedures
- Incident response protocols
- Third-party vendor security requirements
Cyber incident response plan: A playbook for responding to breaches, including:
- Incident response team roles
- Communication procedures
- Evidence preservation steps
- External contact list (IT forensics, legal counsel, PR firm)
- Customer notification processes
Security awareness training records: Proof of regular employee training on:
- Phishing awareness
- Password security
- Social engineering tactics
- Data handling
- Incident reporting
Annual training is minimum; quarterly is increasingly preferred. Many insurers want to see training completion rates above 90%.
IT asset inventory: Current documentation of all systems, applications, and data repositories. You can’t protect what you don’t know you have.
Network Security Assessment Requirements
Most insurers now require a third-party security assessment or vulnerability scan before binding coverage. This might include:
External vulnerability scanning: Automated scanning of your public-facing infrastructure for known vulnerabilities. Many insurers include this free as part of the application process using partners like SecurityScorecard or BitSight.
Security questionnaire: Detailed questions about your security controls, often 50-100 questions covering technical controls, processes, and governance.
Penetration testing: For higher coverage limits (typically $5M+), some insurers require annual penetration testing by certified professionals.
Cyber hygiene score: Third-party ratings based on public information about your security posture. Poor scores can result in declined applications or increased premiums.
What Happens If You Don’t Meet Requirements
Failing to meet these prerequisites doesn’t always mean outright denial. Insurers might:
Offer coverage with exclusions: You might get a policy that excludes ransomware coverage if your backups are insufficient, or excludes email compromise if you lack adequate email security.
Require remediation within 30-60 days: Bind coverage contingent on implementing specific controls within a defined timeframe. Failure to comply can void the policy.
Offer reduced limits: Instead of the $3M you requested, you might only qualify for $1M until security improves.
Quote significantly higher premiums: Adding a 50-100% surcharge for elevated risk is common when controls are weak.
The bottom line: investing in security before you need insurance is both cheaper and more effective than trying to implement everything during the application process.
Navigating the Claims Process
When a cyber incident occurs, how you handle the first 24-48 hours can determine whether your claim is approved or denied. Here’s the reality of the claims process based on recent Australian SMB experiences.
Immediate Steps After an Incident
Don’t start recovery on your own: This is the number one mistake that complicates claims. Your policy likely requires you to contact the insurer’s incident response hotline immediately. Starting restoration before forensics can destroy evidence needed to process your claim.
Call the 24/7 breach response hotline: Every cyber policy includes an emergency response number. Call it immediately—even outside business hours. The response team will:
- Assign a claims adjuster
- Connect you with approved IT forensics firms
- Engage legal counsel for breach notification requirements
- Activate crisis communications support if needed
For Australian businesses, ensure your policy includes local response teams. A Sydney-based forensics team can be on-site within hours; waiting for someone from the US adds critical delays.
Preserve evidence: Don’t shut down or restart affected systems until forensics teams advise. Don’t delete logs or forensic artifacts. Document everything about the incident timeline.
Activate your incident response plan: This is where that documented plan insurers required proves valuable. Your team should know their roles without scrambling.
Documentation Insurers Require
Throughout the incident, you’ll need to provide extensive documentation:
Incident timeline: Detailed chronology of discovery, containment, and recovery efforts. Time-stamped entries showing when systems were affected and what actions were taken.
Financial impact records:
- Business interruption: Daily revenue figures, customer order impacts, employee productivity losses
- Recovery costs: Invoices from forensics firms, legal counsel, PR agencies, IT restoration work
- Third-party impacts: Customer notification costs, credit monitoring services, regulatory response expenses
Evidence of policy compliance: Remember those security controls you confirmed during application? Insurers will verify them:
- MFA logs showing it was active and enforced
- Backup logs showing recent successful backups
- Patch management reports showing systems were current
- Training records showing employees completed security awareness
If you claimed to have EDR deployed but can’t produce evidence it was active on affected systems, expect claim complications.
Communications log: Record of all stakeholder communications—customers, regulators, media, business partners. This supports crisis management cost claims.
Common Claim Denial Reasons
Understanding why claims get denied helps you avoid these pitfalls:
Material misrepresentation on application: If you claimed to have MFA implemented but didn’t, or said backups were tested when they weren’t, insurers can deny the claim entirely. This isn’t minor discrepancies—it’s substantive misstatements about security controls.
Failure to maintain required controls: The security posture you had at application must be maintained throughout the policy period. Letting MFA lapse, stopping employee training, or ceasing backup testing can void coverage.
Unreasonable delays in notification: Most policies require incident notification within 24-72 hours of discovery. Waiting two weeks to report because you wanted to “handle it internally” can jeopardize coverage.
Excluded attack vectors: If your policy excludes social engineering fraud (business email compromise) and that’s how funds were stolen, you’re not covered. Read your exclusions carefully.
Prior knowledge of vulnerabilities: If you knew about unpatched critical vulnerabilities and didn’t remediate them, attacks exploiting those vulnerabilities might be excluded under “known risk” clauses.
Typical Claims Timeline
Understanding the timeline helps set realistic expectations:
Days 1-3: Initial response phase
- Contact insurer hotline
- Forensics team engaged
- Immediate containment actions
- Preliminary scope assessment
Days 4-14: Investigation and containment
- Forensics investigation underway
- Root cause analysis
- Full scope determination
- Recovery planning
- Regulatory notification (if required under NDB scheme)
Days 15-45: Recovery and restoration
- System restoration from backups
- Security remediation
- Business operations return to normal
- Ongoing documentation of costs
Days 46-90: Claims settlement
- Final forensics reports submitted
- All cost documentation provided
- Claims adjuster reviews evidence
- Settlement negotiations
- Payment processing
For straightforward claims with good documentation, payment can occur within 60-90 days. Complex claims involving third-party litigation might take 6-12 months to fully resolve.
Australian Regulatory Considerations During Claims
Notifiable Data Breaches scheme: If the incident is likely to result in serious harm to individuals whose personal information was involved, you must notify the OAIC and affected individuals as soon as practicable. Your insurer’s legal team will help navigate this, but you can’t delay notification to negotiate claim terms.
Privacy Act obligations: Your obligations to secure personal information continue during the incident. The remediation plan must address how you’ll prevent recurrence.
Industry-specific reporting: Healthcare providers may need to notify the Australian Digital Health Agency; financial services might need to report to APRA. Your insurer should help coordinate these notifications.
Choosing the Right Insurer for Your Australian SMB
The cyber insurance market in Australia includes global insurers, domestic specialists, and new entrants. Making the right choice involves more than comparing premiums.
Major Players in the Australian Market
International insurers with Australian presence:
- AIG: Strong in mid-market SMBs, comprehensive coverage options, established claims process
- Chubb: Premium positioning, excellent for higher-limit policies, rigorous underwriting
- AXA: Competitive pricing, good for smaller SMBs, strong European backing
- Travelers: Growing Australian presence, technology sector focus, innovative coverage options
Australian-based insurers:
- QBE: Strong local knowledge, good for businesses wanting Australian-based claims handling
- Suncorp: Accessible for smaller SMBs, often bundled with existing business insurance
- IAG (CGU brand): Competitive pricing, suitable for smaller coverage amounts
Specialist cyber insurers:
- Coalition: Tech-focused approach, includes active security monitoring, transparent pricing
- Corvus: Advanced analytics-based underwriting, security tool integrations, modern platform
What to Evaluate Beyond Price
Incident response network quality: Who are the approved forensics firms, legal counsel, and PR agencies? Australian SMBs should prioritize insurers with local response networks. A forensics team in Melbourne beats waiting for someone to fly from Singapore.
Claims payment track record: Research the insurer’s claims approval rate and average settlement time. Industry contacts, brokers, and online communities can provide insights beyond marketing materials.
Security resources included: Some insurers provide proactive security value:
- Free vulnerability scanning
- Security awareness training platforms
- Threat intelligence feeds
- Incident response tabletop exercises
- Security improvement roadmaps
Policy flexibility: Can you adjust coverage mid-term as your business grows? Are there options to add coverage for emerging risks?
Stability and financial strength: Check the insurer’s financial rating through agencies like Standard & Poor’s or AM Best. You want an A-rated insurer that will definitely be around to pay claims.
Working with Insurance Brokers
For most Australian SMBs, working with a broker specializing in cyber insurance is worthwhile:
Market access: Brokers can quote multiple insurers simultaneously, finding the best coverage-to-cost ratio for your specific situation.
Application assistance: They help you complete security questionnaires accurately, present your security posture favorably, and avoid unintentional misrepresentations.
Claims advocacy: When incidents occur, brokers advocate on your behalf with the insurer, helping ensure documentation is complete and settlement is fair.
Policy comparison: Brokers can explain subtle differences between policies that affect real-world coverage, not just highlight premium differences.
Broker commissions typically come from insurers (10-15% of premium), not directly from you, though this is built into overall pricing.
Next Steps: Getting Covered
If you don’t currently have cybersecurity insurance, here’s a practical roadmap:
1. Assess your current security posture (Week 1): Before approaching insurers, honestly evaluate your controls against the prerequisites outlined earlier. Identify gaps in MFA, EDR, backups, and documentation.
2. Implement critical security controls (Weeks 2-6): Address major gaps that would result in application denial:
- Deploy MFA on all remote access and cloud email
- Implement EDR on all endpoints
- Establish offline/immutable backups with testing schedule
- Document your incident response plan
3. Prepare required documentation (Week 7): Gather the materials insurers will request:
- IT asset inventory
- Information security policy
- Employee training records
- Current backup test results
4. Engage an insurance broker (Week 8): Find a broker experienced with cyber insurance for Australian SMBs. Ask for referrals from your professional network or industry associations.
5. Complete applications and compare quotes (Weeks 9-10): Your broker will submit applications to multiple insurers. Compare not just premiums but coverage breadth, limits, deductibles, and response network quality.
6. Review policy carefully before binding (Week 11): Read the actual policy document, not just the summary. Pay special attention to exclusions, sub-limits, and conditions precedent.
7. Implement ongoing compliance (Ongoing): Maintain the security controls you confirmed in your application. Schedule quarterly reviews to ensure MFA is enforced, backups are tested, training is current, and patches are applied.
For Australian SMBs operating without cybersecurity insurance in 2024, the question isn’t whether you can afford coverage—it’s whether you can afford to operate without it. A single ransomware incident can cost $100,000 to $500,000 to remediate for a typical SMB, and that’s before considering business interruption losses, customer notification costs, and potential regulatory fines.
The evolving threat landscape, combined with stricter Australian privacy requirements, makes cyber insurance an essential component of your business resilience strategy. By understanding what’s covered, meeting insurer prerequisites, and choosing the right policy for your specific risks, you transform insurance from a confusing overhead into a genuine safety net when the inevitable occurs.
Need help implementing the security controls insurers require before you can get covered? CloudGeeks specializes in helping Australian SMBs build cybersecurity foundations that both protect your business and meet insurance requirements. Contact us to discuss your security and insurance readiness.
