IT Compliance Requirements for Australian Financial Services

IT Compliance Requirements for Australian Financial Services
Australian financial services firms operate in one of the most regulated IT environments in the country. From banks and insurers to financial advisers and mortgage brokers, the regulatory framework for information security and IT governance is comprehensive and continues to evolve.
The Optus and Medibank breaches in 2022 intensified regulatory scrutiny across all sectors, but financial services faces the highest expectations. Regulators expect not just compliance with specific standards but a culture of security that permeates every aspect of IT operations.
This guide covers the key IT compliance requirements that Australian financial services firms must address, with practical guidance for small and medium-sized firms that may not have dedicated compliance teams.
The Regulatory Landscape
APRA Prudential Standard CPS 234: Information Security
Who it applies to: APRA-regulated entities including authorised deposit-taking institutions (banks, building societies, credit unions), general insurers, life insurers, and registrable superannuation entities.
What it requires:
CPS 234, which came into effect on 1 July 2019, requires APRA-regulated entities to:
- Maintain an information security capability commensurate with the size and extent of threats to their information assets
- Implement controls to protect information assets commensurate with the criticality and sensitivity of those assets
- Systematically test the effectiveness of security controls through a testing program
- Notify APRA of material information security incidents within 72 hours (and within 10 business days for material control weaknesses)
Key obligations:
- Information asset management: Identify, classify, and manage information assets (data, systems, infrastructure) based on criticality and sensitivity.
- Information security capability: Maintain security resources (people, processes, technology) commensurate with your risk profile.
- Policy framework: Maintain an information security policy framework that is reviewed at least annually.
- Information asset identification and classification: Classify all information assets by criticality and sensitivity.
- Implementation of controls: Deploy controls that protect confidentiality, integrity, and availability.
- Incident management: Maintain and test an incident management plan.
- Testing: Systematically test the effectiveness of security controls.
- Internal audit: Engage competent internal audit to review information security controls.
Australian Privacy Act 1988 and APPs
Who it applies to: Organisations with annual turnover exceeding three million dollars, as well as health service providers, organisations trading in personal information, and others regardless of turnover.
Key requirements for financial services:
- Australian Privacy Principles (APPs): 13 principles governing the collection, use, disclosure, storage, and destruction of personal information.
- Notifiable Data Breaches (NDB) scheme: Mandatory notification to the OAIC and affected individuals when an eligible data breach occurs.
- Credit Reporting Privacy Code: Additional obligations for organisations involved in credit reporting.
Anti-Money Laundering and Counter-Terrorism Financing Act 2006 (AML/CTF)
IT implications:
- Customer identification and verification systems must be secure and auditable
- Transaction monitoring systems must be protected from tampering
- Records must be retained for seven years with appropriate access controls
- Systems must support suspicious matter reporting to AUSTRAC
ASIC Regulatory Requirements
The Australian Securities and Investments Commission (ASIC) has increasingly focused on cyber resilience for financial services firms. ASIC’s Cyber Resilience Good Practices guidance (Report 429) outlines expectations for:
- Governance and risk management
- Identification and protection of key assets
- Detection, response, and recovery capabilities
- Information sharing and collaboration
While ASIC has not issued specific binding standards equivalent to CPS 234, regulated entities should treat ASIC’s guidance as setting baseline expectations, particularly as ASIC has indicated cyber resilience is a supervisory priority.
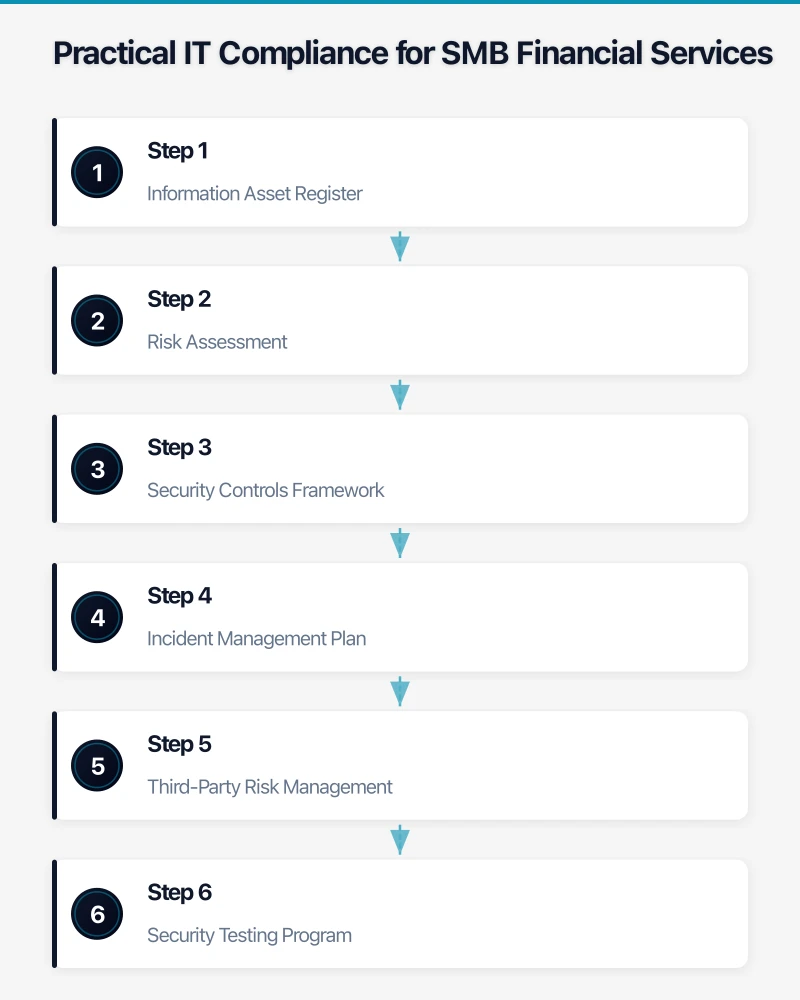
Practical IT Compliance for SMB Financial Services
Step 1: Information Asset Register
Create and maintain a register of all information assets. For a small financial services firm, this includes:
Data assets:
- Client personal information (names, addresses, dates of birth)
- Financial data (account numbers, transaction history, tax file numbers)
- Identification documents (driver’s licences, passports)
- Financial advice records and statements of advice
- Internal business data (HR records, financial reports)
System assets:
- Client management system or CRM
- Financial planning software
- Accounting software
- Email and collaboration platforms
- File storage systems
- Websites and client portals
Infrastructure assets:
- Servers (on-premises and cloud)
- Network equipment (firewalls, switches, wireless access points)
- End-user devices (laptops, desktops, mobile devices)
- Backup systems
For each asset, record:
- Asset owner
- Classification (public, internal, confidential, restricted)
- Storage location
- Access controls in place
- Backup and recovery arrangements
Step 2: Risk Assessment
Conduct a risk assessment focused on information security threats. Common risks for small financial services firms include:
- Phishing and social engineering: Staff tricked into revealing credentials or authorising fraudulent transactions
- Ransomware: Encryption of critical business data with extortion demands
- Insider threats: Disgruntled or careless employees accessing or leaking client data
- Third-party breaches: Compromise of software vendors, cloud providers, or service providers
- Lost or stolen devices: Laptops or mobile devices containing client information
- Misconfiguration: Cloud services or applications configured with excessive permissions
Assess each risk for likelihood and impact, and document the controls you have in place or plan to implement.
Step 3: Security Controls Framework
Align your security controls with both CPS 234 requirements and the ACSC Essential Eight. This dual alignment addresses regulatory expectations while implementing proven mitigation strategies.
Access controls:
- Multi-factor authentication for all users on all systems
- Role-based access control (least privilege principle)
- Regular access reviews (quarterly for sensitive systems)
- Prompt removal of access when staff depart
- Privileged access management for administrator accounts
Data protection:
- Encryption of data at rest and in transit
- Data loss prevention (DLP) policies for email and file sharing
- Secure disposal of data and devices
- Classification labelling for sensitive documents
Network security:
- Business-grade firewall with current firmware
- Network segmentation between office, guest, and server networks
- Intrusion detection or prevention systems
- Secure remote access (VPN or Zero Trust)
Endpoint security:
- Managed antivirus and endpoint detection and response (EDR)
- Device encryption (BitLocker for Windows, FileVault for Mac)
- Patch management (operating system and application updates within 48 hours for critical vulnerabilities)
- Mobile device management for phones and tablets accessing corporate data
Email security:
- Advanced anti-phishing protection
- SPF, DKIM, and DMARC email authentication
- Email encryption capability for sensitive communications
- Attachment sandboxing
Step 4: Incident Management Plan
CPS 234 requires a documented and tested incident management plan. Your plan should cover:
Detection:
- How security incidents are identified (monitoring, user reports, third-party notifications)
- Who receives initial alerts and how
- Classification criteria for incident severity
Response:
- Roles and responsibilities for incident response
- Communication procedures (internal and external)
- Containment actions for common incident types
- Evidence preservation requirements
Notification:
- APRA notification within 72 hours for material incidents
- OAIC notification for eligible data breaches under the NDB scheme
- Client notification requirements
- ASIC notification if applicable
- Law enforcement notification via the ACSC or Australian Federal Police
Recovery:
- System restoration procedures
- Data recovery from backups
- Business continuity arrangements
- Post-incident review process
Test your incident management plan at least annually through tabletop exercises or simulations.
Step 5: Third-Party Risk Management
CPS 234 extends to third-party service providers, including cloud providers and managed service providers. You must:
- Assess the information security capability of third parties before engagement
- Include information security requirements in contracts and service level agreements
- Monitor third-party compliance with security requirements
- Ensure you can access audit reports or certifications (SOC 2, ISO 27001)
For cloud services, verify:
- Data is stored in Australian data centres
- The provider has appropriate security certifications
- You can retrieve your data if the relationship ends
- The provider will notify you of security incidents affecting your data
Step 6: Security Testing Program
CPS 234 requires systematic testing of security controls. For small financial services firms, a practical testing program includes:
Ongoing (automated):
- Vulnerability scanning of external-facing systems (monthly)
- Email phishing simulations (quarterly)
- Patch compliance monitoring (continuous)
Periodic (manual):
- External penetration testing (annually)
- Security configuration review (annually)
- Access rights review (quarterly)
- Backup restoration testing (quarterly)
- Incident response plan test (annually)
As needed:
- Testing after significant changes to systems or infrastructure
- Testing after a security incident to verify remediation
- Testing of new systems before deployment
Step 7: Documentation and Evidence
Regulatory compliance requires documentation. Maintain records of:
- Information security policy (reviewed annually)
- Risk assessments and treatment plans
- Asset register and classifications
- Incident reports and post-incident reviews
- Testing results and remediation actions
- Training records for staff
- Third-party assessments and contracts
- Board or senior management reporting on information security
Store this documentation securely and ensure it is accessible for audits and regulatory inquiries.
Common Compliance Gaps for Small Firms
Based on common findings, small financial services firms often have gaps in:
- Formal documentation: Security practices may exist informally but are not documented in policies and procedures.
- Testing programs: Controls exist but are not systematically tested and validated.
- Third-party assessments: Cloud services and software providers are engaged without formal security assessment.
- Incident response preparedness: No documented plan, or the plan has never been tested.
- Board reporting: Senior management receives no regular reporting on information security posture.
- Access reviews: User access is not periodically reviewed, leading to excessive permissions.
Addressing these gaps is typically more about process and documentation than technology investment.
Getting Help
Many small financial services firms lack the internal resources for comprehensive IT compliance. Options include:
- Managed IT services provider: Outsource security operations and monitoring to a provider experienced with financial services compliance.
- Virtual CISO (vCISO): Engage a part-time chief information security officer to guide your compliance program.
- Compliance consultants: Engage specialists for specific projects like risk assessments, policy development, or penetration testing.
- Industry associations: The Financial Services Council, Stockbrokers and Financial Advisers Association, and other bodies provide guidance and resources.
The cost of engaging external expertise is typically far less than the penalties, remediation costs, and reputational damage associated with a compliance failure or data breach.
Moving Forward
IT compliance for Australian financial services is not a one-time project. It requires ongoing attention, regular review, and continuous improvement. Start by addressing the highest-risk gaps, build your documentation, and establish a rhythm of regular testing and review.
The regulatory framework is designed to protect both your clients and your business. Treating compliance as a foundation for good security practice, rather than a box-ticking exercise, will serve your firm well as the threat landscape continues to evolve.
